Enterprises are increasingly using hybrid environments, but this move can present risks and challenges, especially for organizations adopting DevOps. How can hybrid environment security fit naturally into develop- ment processes?
Enterprises are harnessing hybrid cloud technologies to power their digital transformation: the integration of flexibility, agility, and unique cultural shifts into business processes to enrich customer and stakeholder experience. Gartner predicts that by 2020, 90 percent of organizations will be adopting or using hybrid cloud infrastructures and services (i.e. using multiple cloud services).1 The hybrid cloud environment enables businesses to portably manage workload requirements by using public cloud platforms to run applications, while using the resources of private cloud infrastructures to manage the data needed to run the applications.
Hybrid cloud security accordingly has unique requirements. And given how this technology enables workloads to be run on different platforms and environments – from on-premises to private and public infrastructures – traditional and defined security will inevitably fall short. Also, with the adoption of containers and microservices, securing workloads can be seemingly complicated. For enterprises adopting DevOps, it can be especially challenging to incorporate security into an approach that focuses on rapid development and delivery across cloud instances and containers. While it helps meet tight timetables, DevOps can also run the risk of overlooking security. Trend Micro’s Hybrid Cloud Security platform helps security teams address the challenges that stem from using hybrid environments.
The threat landscape
Today’s threat landscape can be a challenge for enterprises. In the first half of 2018 alone, 47 new cryptocurrency-mining malware families and 118 new ransomware families were seen.2 Threats are also diversifying into infrastructures that are critical to enterprises, like web servers and application development platforms. In 2017, for instance, the Erebus Linux ransomware hit a South Korean web development company and affected 153 Linux servers and more than 3,400 businesses. The impact: over USD 1 million in losses as well as damaged reputation and a costly remediation process.3 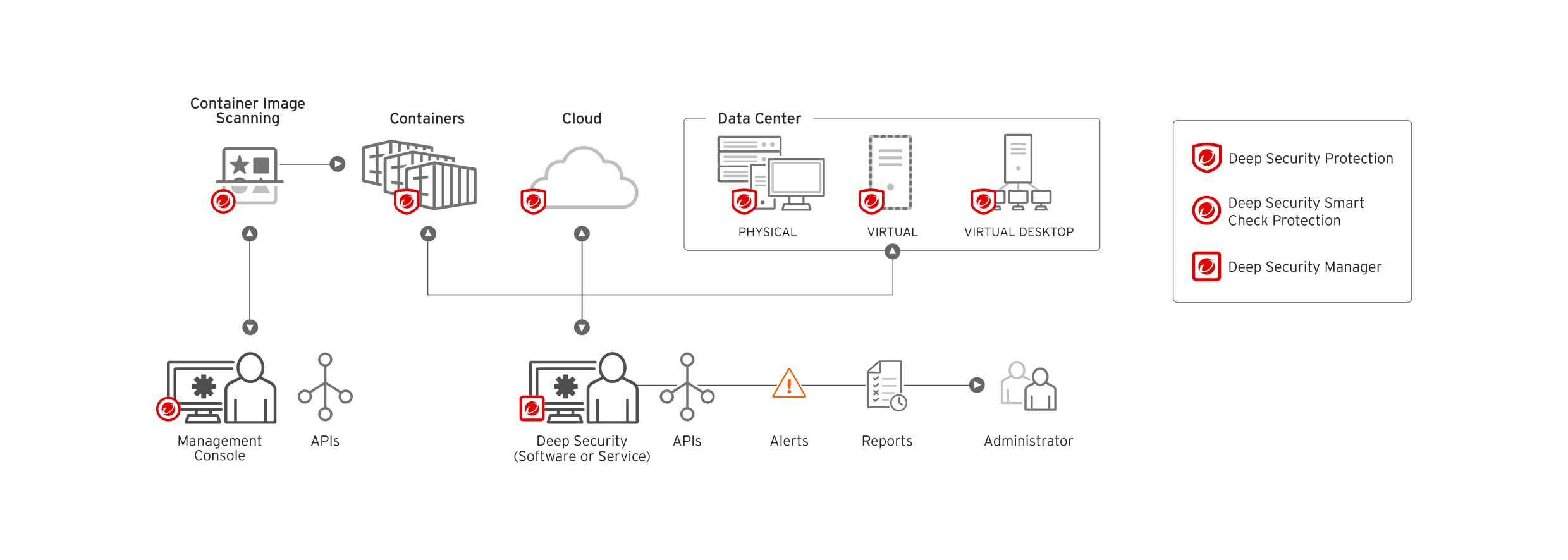
Fig. 1: A consolidated solution with multiple security tools lowers the maintenance, budget, and overhead associated with support and operational functions. Deep Security provides API integrations to seamlessly build across leading cloud, virtualization, container and data center environments.
Indeed, cloud workloads require a security strategy that can navigate today’s evolving and ever-increasing threats. For customer’s security teams, exposure to vulnerabilities and threats translates to adverse impact to their organizations’ bottom lines. The impact is exacerbated when stacked up with stringent compliance requirements, such as the implementation of privacy by design, as mandated by the European Union General Data Protection and Regulation.
For enterprises already adopting DevOps, an unsecure or vulnerable application or software can mean wasted resources, as they have to constantly rework and rebuild them to meet security and compliance requirements. Integrating security early into the development life cycle significantly reduces disruptions while helping IT and DevOps teams address security gaps or misconfigurations faster.
Thus, defense-in-depth security capabilities are needed, and they must have visibility across the application or software’s life cycle – from pre-deployment to runtime. For example, security mechanisms such as intrusion detection and prevention systems (IDS/IPS) and firewalls help thwart network-based threats and exploits, while application control deters anomalous executables and scripts from running. It is projected that by 2022, application control will be employed in 60 percent of server workloads.4 For DevOps teams, baking in security into the development life cycle means security as code. This can be achieved through scalable application programming interfaces (APIs) and scripts designed with security from the first build in order to minimize superfluous work.
Breaking up siloes
As mentioned before, more than 90 percent of enterprises will be employing a multi-cloud strategy for their workloads by 2020.5 And despite the increasing popularity of containers in application development, organizations will continue to use other virtualization technologies and computing platforms, like on-premises or physical software and servers, virtual machines, and even serverless infrastructures. Furthermore, many enterprises are also expected to use a combination of traditional and cloud-based services for their operations.
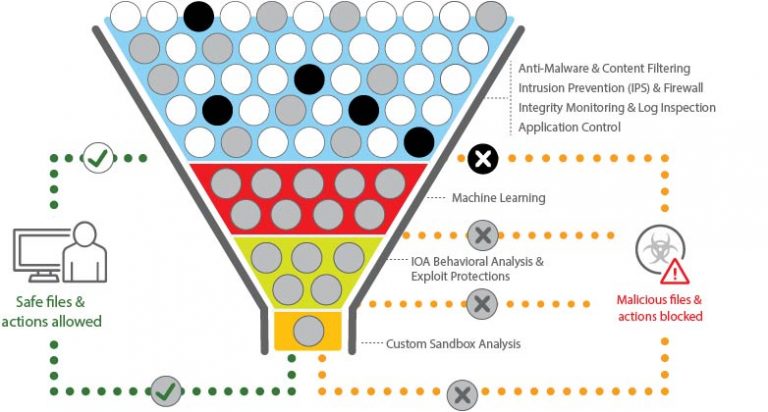
Fig. 2: A cross-generational blend of threat defense techniques protects runtime physical, virtual, cloud, and container workloads, as well as scanning of container images in the software build pipeline.
Incorporating security across these multiple computing platforms can pose a challenge. IT teams have to juggle different and incompatible security tools, which unnecessarily create convolution in their management. This unwanted complexity can also mean higher overhead by possibly slowing down incident response, as siloed and disparate platforms will drive security teams to manually monitor each of them. This, in turn, creates bottlenecks in incident and compliance reporting. From a DevOps perspective, siloed teams and tools create blind spots, as security may tend to be neglected (such as overlooking vulnerabilities in the code) as they rush to deploy applications faster.
An effective security strategy thus ensures visibility into the applications and their underlying infrastructures, consistency in their security, and adaptability across various environments. Visibility across multiple environments is a major concern6 for enterprises: It gives organizations governance over the underlying infrastructures or platforms that they use to host, run, and manage their workloads. In turn, security teams can streamline the processes for audits, compliance reporting, and risk management. Security tools should be easily integrated across various computing environments but must be also purpose-built for the platform on which DevOps teams create and deploy their ap- plications.
Trend Micro Deep Security combines the capabilities of multiple security tools, reducing the number of point solutions and providing a single dashboard with full visibility into leading environments like AWS, Google Cloud, Microsoft Azure, and VMware. The platform lowers the cost and complexity of securing workloads across multiple environments by providing different flexible purchase options. This allows for automation of security operations, via extensive application programming interface (API) integration, and offering security capabilities that can virtually shield servers from the latest advanced threats like ransomware and network-based vulnerabilities.
Automation and agility
Automation is not just a buzzword: It has become a necessity for many organizations as they further streamline their workload processes to keep pace with a constantly changing technology landscape. Hybrid environments, through containers and other microservices, empower enterprises with the scalability needed to flexibly deploy and monitor servers or applications. And when thousands of these servers or applications need to be concurrently run or configured, automation becomes vital. Furthermore, in DevOps, automation means ensuring consistency through optimized and iterative processes, enabling companies to deploy applications faster across cloud platforms.
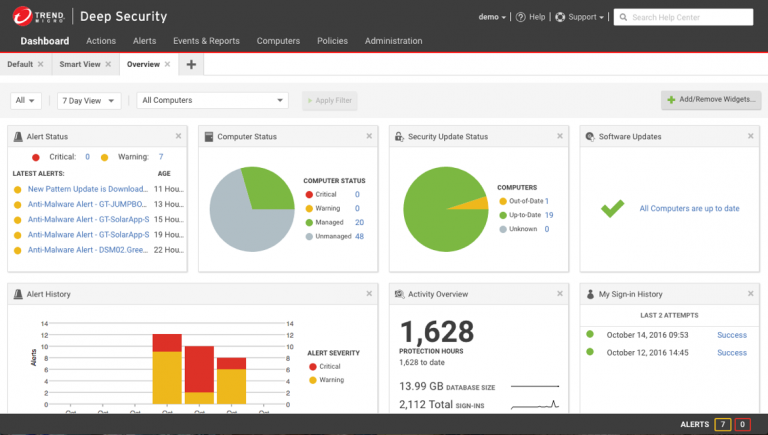
Fig. 3: Centralized visibility accelerates incident response through intuitive dashboards and actionable insights. This is required to manage risk and meet compliance.
However, as organizations focus on deploying applications as fast as possible, particularly those adopting DevOps, security is being misconstrued as something that can slow down the development life cycle. A perceived lack of security adoption can be ascribed to how it is sometimes misconceived as a roadblock.7 As businesses try to meet time-to-market deadlines, security becomes an afterthought or may even be circumvented.
Automated security tools enable organizations to integrate security into the DevOps process and toolchain (orchestration, monitoring, continuous delivery, and IT service management). This helps ensure that security is adopted throughout the development life cycle without causing unnecessary friction between development and operations teams. For DevOps teams, automated security helps accelerate lifecycles while also alleviating the burden of manually testing the application for vulnerabilities or threats. It’s thus unsurprising that 59 percent of surveyed organizations are automating security into their DevOps processes.8 Deep Security helps to defend cloud workloads, addressing the need to protect what is deployed in the cloud as a part of the shared security responsibility for the cloud. It provides elastic security for dynamic workloads running in AWS, Azure, Google Cloud, and more. Deep Security’s REST APIs allow for security to be integrated with existing toolsets, enabling automated security deployment, policy management, health checks, compliance reporting, and more. The supported tools include:
– Orchestration tools: Chef, Puppet®, Ansible, AWS Op- sWorks, SaltStack®, Kubernetes®
– Monitoring tools: New Relic®, AWS CloudTrail®, AWS Config
– Continuous delivery: GitHub®, Jenkins®
– IT service management: ServiceNow, Jira®, Slack®
Security in hybrid cloud environments
Hybrid environments provide organizations with agility and efficiency while also reducing costs. But leaving them exposed to threats can have adverse ramifications to an organization’s bottom line, which is why securing them is of great importance. Fortunately, organizations are realizing this at an increasing rate. While incorporating security and implementing best practices into workload processes and development life cycles can be a daunting challenge, it can empower enterprises to be more resilient against threats while keeping pace with the need to innovate.
Trend Micro’s Hybrid Cloud Security solution provides streamlined and automated security integrated into an organization’s DevOps pipeline while delivering multiple cross-generational threat defense techniques for protecting runtime physical, virtual, and cloud workloads. It also adds protection for containers via Deep Security and Deep Security Smart Check, including the scanning of container images during pre-deployment and host and Kubernetes protection at runtime across cloud workloads and hybrid servers.
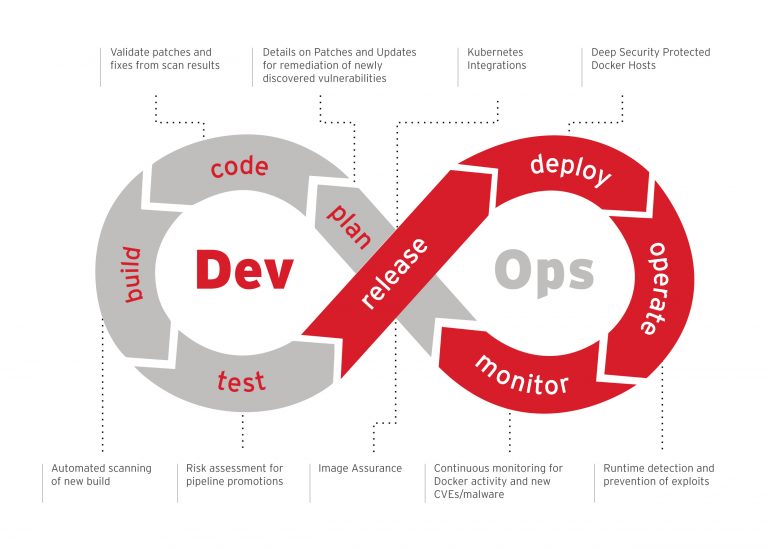
Fig. 4: Security is moving left and covers the entire DevOps processes with both build-time image scanning and runtime workload protection.
These solutions enable organizations to focus on security and compliance while still moving in the agile and adaptable world of DevOps. With multiple security capabilities and a single dashboard to grant full visibility across hybrid environments they also reduce the number of security tools needed. Trend Micro Deep Security lowers the cost and complexity of securing workloads across multiple environments, with simple procurement and consolidated billing though the AWS and Microsoft Azure Marketplaces.
Sources
– 1. https://www.gartner.com/en/newsroom/press- releases/2017-04-05-gartner-says-a-massive-shift-to- hybrid-infrastructure-services-is-underway
– 2. https://www.trendmicro.com/vinfo/us/security/ research-and-analysis/threat-reports/roundup/ unseen-threats-imminent-losses
– 3. https://blog.trendmicro.com/trendlabs-security- intelligence/erebus-resurfaces-as-linux-ransomware/
– 4. Gartner, Market Guide for Cloud Workload Protec- tion Platforms, 26 March 2018.
– 5. https://www.gartner.com/en/newsroom/press- releases/2017-04-05-gartner-says-a-massive-shift-to- hybrid-infrastructure-services-is-underway
– 6. https://www.csoonline.com/article/3198008/hide- and-seek-security-teams-lack-visibility-in-the-cloud. html
– 7. https://www.wired.com/insights/2013/10/ mythbusting-devops-and-security/
– 8. https://www.infosecurity-magazine.com/news/ developers-outnumber-security-pros/

Hannes Steiner, Senior Director Sales
Hannes leads the German sales team at Japanese cybersecurity vendor Trend Micro. He helps customers secure their infrastructures in a rapidly evolving technological environment.
Trend Micro Deutschland GmbH
Parkring 29
85748 Garching bei München
salesinfo_de@trendmicro.com

